Artificial intelligence can be a helpful and efficient tool for organizations to use in sifting through massive amounts of data. However, the adoption of AI and machine learning technology is a continuous journey, not an endpoint, cybersecurity experts say.
AI/ML algorithms have to be trained by human operators and specifically tailored to the organizations they’re serving – which can be a time consuming process – if they are expected to be successful.
Despite these challenges, AI/ML is becoming more widely used as government and industry make the transition to being data-centric.
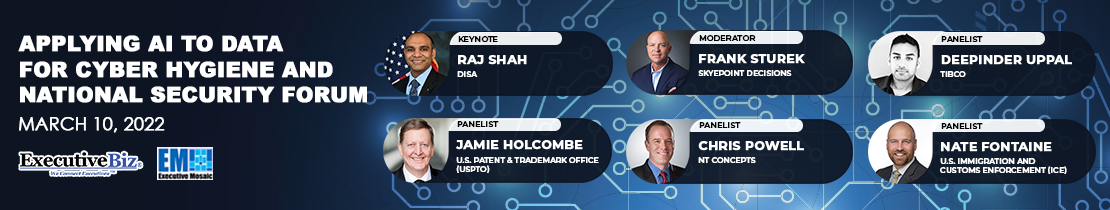
Raju Shah, director of enterprise engineering and governance and senior technologist at the Defense Information Systems Agency, said “we have to change fast,” in order to modernize while keeping pace with the constant influx of data that organizations are seeing today.
Organizations must “leverage data as a center of gravity,” Shah said in his keynote address to ExecutiveBiz Events’ Applying AI to Data for Cyber Hygiene and National Security Forum.
Data and the AI/ML solutions being deployed to understand it are becoming increasingly more critical to large federal agencies as they shore up their cyber defenses and better protect themselves against the growing threat of cyberattacks.
Jamie Holcombe, chief information officer of the U.S. Patent and Trademark Office, said during the forum’s panel discussion that AI is a foundational component of the office’s ability to process its colossal 19 petabytes of data.
“It’s just the plethora of data, it’s just too much,” Holcombe told his audience. But not all of it needs to be protected in the same ways.
At USPTO, Holcombe said he deals with a wide range of data that requires different amounts of security. For example, pre- and post-patent data should be shared with and available to the general public, while pending data is highly confidential and needs higher levels of protection.
Holcombe’s “Jekyll and Hyde” mentality surrounding security posits that organizations should take a more customized approach tailored to their individual data needs and move past the outdated castle-and-moat method, which has proven less effective over time as attackers adapt and evolve.
“The castle walls are rapidly eroding, especially in the government,” commented Nate Fontaine, chief of the governance and risk management branch of the Immigration and Customs Enforcement within the Department of Homeland Security.
The drastic and abrupt shift toward remote work due to the onset of the COVID-19 pandemic two years ago posed new challenges for organizations as their cybersecurity nets were stretched to protect an array of users and systems across multiple locations worldwide.
“Now, you’ve got to virtually protect those individual devices and you no longer have that medieval analogy of huge castle walls and moats built around yourselves,” Fontaine explained.
Despite the deep issues it uncovered, the rise of remote work did have its benefits, said Chris Powell, chief technology officer of NT Concepts.
“The work from home mentality allowed us to increase our cyber hygiene practices. There was better cyber awareness training in that information,” Powell said, explaining that remote work unveiled an opportunity for organizations to educate their employees on best practices.
A tactical aspect of bolstered cyber hygiene, Powell explained, is managing and tracking how and when users access data. “There’s no doubt that maintaining a current IT asset inventory allows us to understand what devices are on our network and make sure that there are no unmanaged assets,” he stated.
Especially across a disparate workforce of thousands of individuals, knowing when, where and by whom your data is being accessed is essential. Now, these same principles are being applied in military applications and in organizations that need to get timely data to operators in the field.
Federal and industry organizations are departing from the antiquated castle-and-moat methodology as the need to expand their offerings to agents in the field increases. However, though the need to push out capabilities to the tactical edge is growing, the knowledge of how to accomplish this expansion is not.
Deepinder Uppal, chief innovation and technology officer of TIBCO, said there is a general understanding in the cyber industry of how to deploy cyber hygiene elements to protect local endpoints and core systems while providing appropriate system access to users who need it.
“What’s less cohesively, or rather consistently understood is how to do that on the edge or how to do that with systems that are connected out to commercial products,” Uppal said. “What can we put in place to defend those endpoints, which are often thought to be the weakest across the DOD spectrum?”
As agencies start their digital transitions, they should incorporate the internet of things within their infrastructure so that they can start to leverage IoT across today’s battlespace, Uppal posited.

Learn more about artificial intelligence applications at the Potomac Officers Club’s 4th Annual AI Summit this spring!
David Spirk, chief data officer at the Department of Defense, is scheduled to keynote the summit, which annually features an elite roster of government and industry officials to speak on the most pressing AI topics of today.





